The Hedera marketing email got hacked and used for phishing attacks, a critical vulnerability on MoveIt was patched, plus a $70K address poisoning attack.
On June 26 a marketing email for Hedera was hacked, with the attacker sending out phishing emails to the team’s subscribers. Hedera is the developer of Hedera Hashgraph, a proof-of-stake blockchain network launched in 2018.
The team acknowledged the hack in a post to X and warned users not to interact with any links in emails from marketing@hedera.
The marketing@hedera email has been compromised. Do not open any emails or links from this address. We’ll provide more details soon.
— Hedera (@hedera) June 26, 2024
Phishing is a technique where an attacker poses as a trusted source and convinces the user to give away information or to perform an action the attacker desires. In this case, the attacker used the compromised Hedera email to pretend to be a representative of the development team.
The team has not yet disclosed what was in the phishing emails. However, most crypto phishing emails offer the user an enticing reward, such as a token airdrop, if they click on a link to navigate to the attacker’s fake website, which often appears to be from a trusted source. When the user connects to the website with their wallet, they are asked to authorize token approvals to receive the airdrop.
But instead of allowing the user to obtain the airdrop, these approvals allow the attacker to drain the user’s wallet. Users should consider being extra cautious when clicking links from emails, even if the emails come from what appears to be a trusted source. As the Hedera example illustrates, even trusted email addresses can be hacked or spoofed.
The Hedera team promised to provide more details soon. Cryptalb could not determine how much crypto, if any, was lost due to the phishing emails at the time of publication.
White hat corner: MoveIt file transfer vulnerability is patched
Security researchers discovered a critical vulnerability in the MoveIt file transfer software developed by Progress, according to an official bulletin from the software’s development team. However, the vulnerability has been patched in its current version.
Some large businesses use MoveIt Transfer to transfer files between employees. These files could contain customer data, private keys or other sensitive information. According to a report from cybersecurity firm Watchtower Labs, the vulnerability allowed an attacker to impersonate any user on an enterprise’s network as long as the attacker knew the user’s username.
To perform the attack, the hacker needed to supply the server with a username. In response, the server would ask for the user’s private key. But instead of producing the real key (which the attacker presumably wouldn’t know), they could supply a file path containing a fake key they generated themselves.
Because of peculiarities in the way the MoveIt software handled this situation, it would produce an empty string as the public key. As a result, the authentication would appear to fail. However, Watchtower discovered that although the authentication would produce an error message and seem to fail, the crucial “statuscode” variable used to block invalid users would treat the attacker as if they had properly authenticated.
As a result, the attacker would be able to access any files that the real user could access, allowing them to gain sensitive client or customer data.
Progress patched the vulnerability on June 25. However, some businesses may not have upgraded to the latest version yet. The developer stated, “We strongly urge all MOVEit Transfer customers on versions 2023.0, 2023.1 and 2024.0 to upgrade to the latest patched version immediately.”
The company said that MoveIt Cloud is unaffected by the vulnerability, as it has already been patched.
Address poisoning attack
Blockchain security firm Cyvers detected a large address poisoning attack on June 28. The victim lost over $70,000 worth of USDT.
The attack began on June 25, when the victim transferred 10,000 USDT to a Binance deposit address that began with “0xFd0C0318” and ended with “1630C11B.”
Shortly afterward, the attacker sent 10,000 fake USDT from the victim’s account to an account under the attacker’s control. This transfer was not authorized by the victim, but because the fake token contained a malicious transfer function, it was successful.
The address these fake tokens were sent to began with “0xFd0Cc46B” and ended with “6430c11B,” containing the same first six and last four characters as the victim’s Binance deposit address. The attacker likely used a vanity address generator to create this similar-looking address.
Two days later, on June 27, the victim sent 70,000 USDT to this malicious address. The victim probably cut and pasted the address from their transaction history, intending to deposit the funds to Binance. However, Binance did not receive the funds, and they are now in the attacker’s hands.
The Tether development team can freeze wallet addresses holding USDT. However, they will generally only freeze an address after a request from law enforcement. At the time of publication, this wallet still holds USDT and has not yet swapped it for other tokens, so a freeze may have already occurred. If the address has not yet been frozen, there is still time to make a complaint, and the victim may yet get their funds back.
However, it is also possible that the attacker may swap the USDT for Ether or other cryptocurrencies before the address is frozen, in which case the funds will be much more difficult to recover.
Crypto users should be aware that some wallet applications load transaction history directly from the blockchain. As a result, they sometimes show transactions as being from the user when they are, in fact, from a third party. Users are advised to check all characters of an address before sending a transaction, not just the first and last characters.
Unfortunately for this user, they may have learned this lesson at a high price, as they could be $70,000 poorer as a result of this mistake.
Centralized exchanges
On June 22, Istanbul-based crypto exchange BtcTurk was exploited via a stolen private key. The exchange acknowledged the attack on the following day. According to a Google translation, the statement read in part, “Dear user, our teams have detected that there was a cyber attack on our platform on June 22, 2024, which caused uncontrollable [losses] to be taken.”
The exchange stated that the attack was only performed against its hot wallets, and the bulk of its assets remain safe. It also claimed that it has enough “financial strength” to pay back users for the losses and that customer balances will be unaffected.
Cybersecurity firm Halborn estimated that BtcTurk lost over $55 million in the attack.
According to onchain sleuth ZackXBT, the attacker likely deposited 1.96 million AVAX ($54.2 million) to centralized exchanges Coinbase, Binance and Gate, which was subsequently swapped for Bitcoin, as onchain data shows nearly equivalent values of BTC being transferred out of these exchanges right after the AVAX was transferred in.
AVAX fell by 10%, apparently as a result of these swaps.
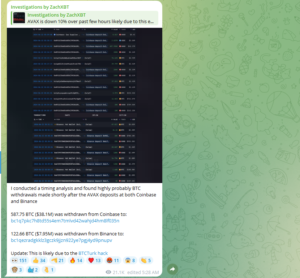
Reported attacker deposits to and from centralized exchanges. Source: (ZachXBT, Telegram)
Since the attack, BtcTurk has launched new hot wallets with private keys that are not under the attacker’s control. The exchange has strongly advised users not to use old deposit addresses, as any funds sent to them will likely be stolen by the attacker. Instead, users should deposit using new addresses found within the app’s interface.












